What’s the Harm: Charting Your Course Version
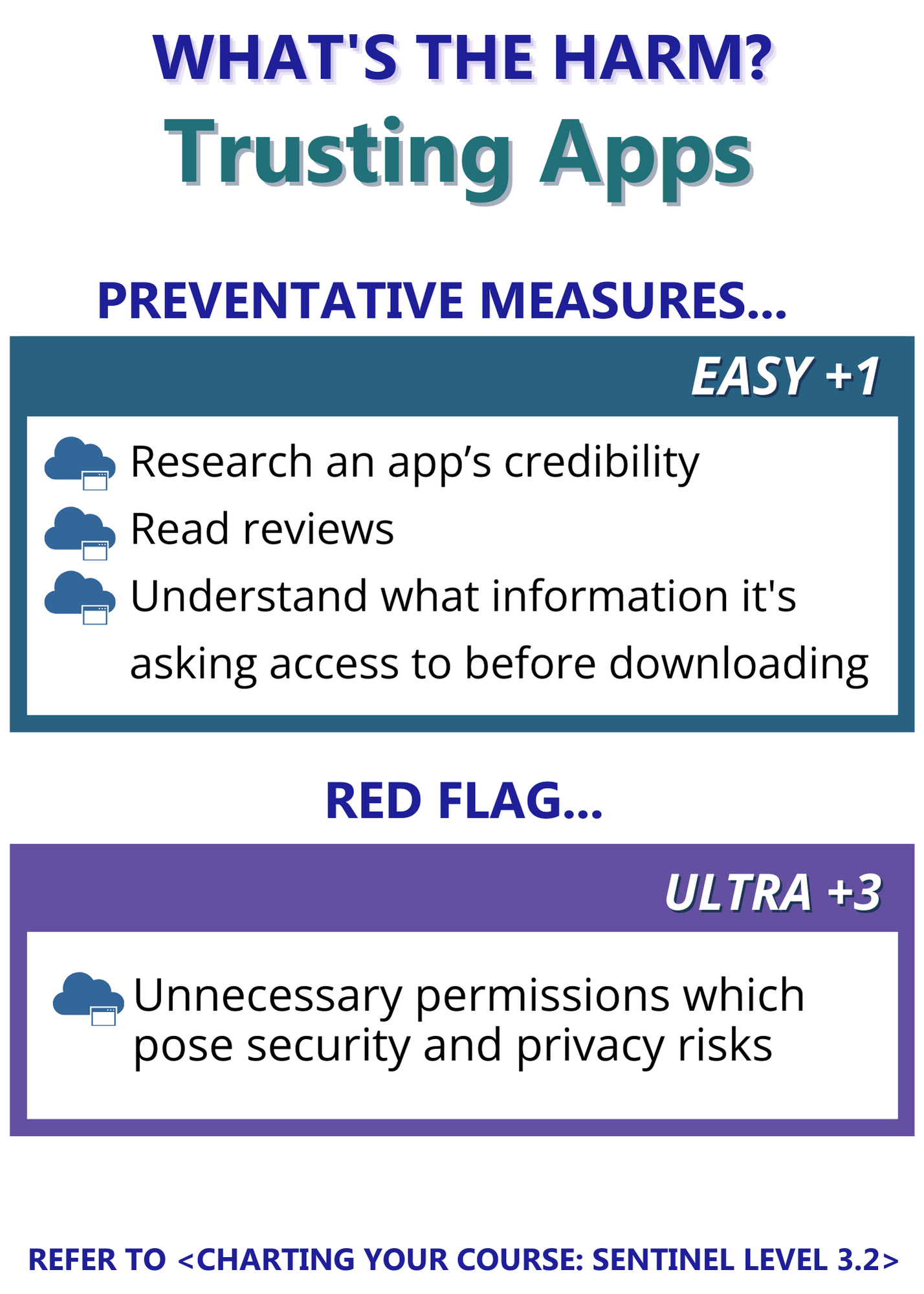
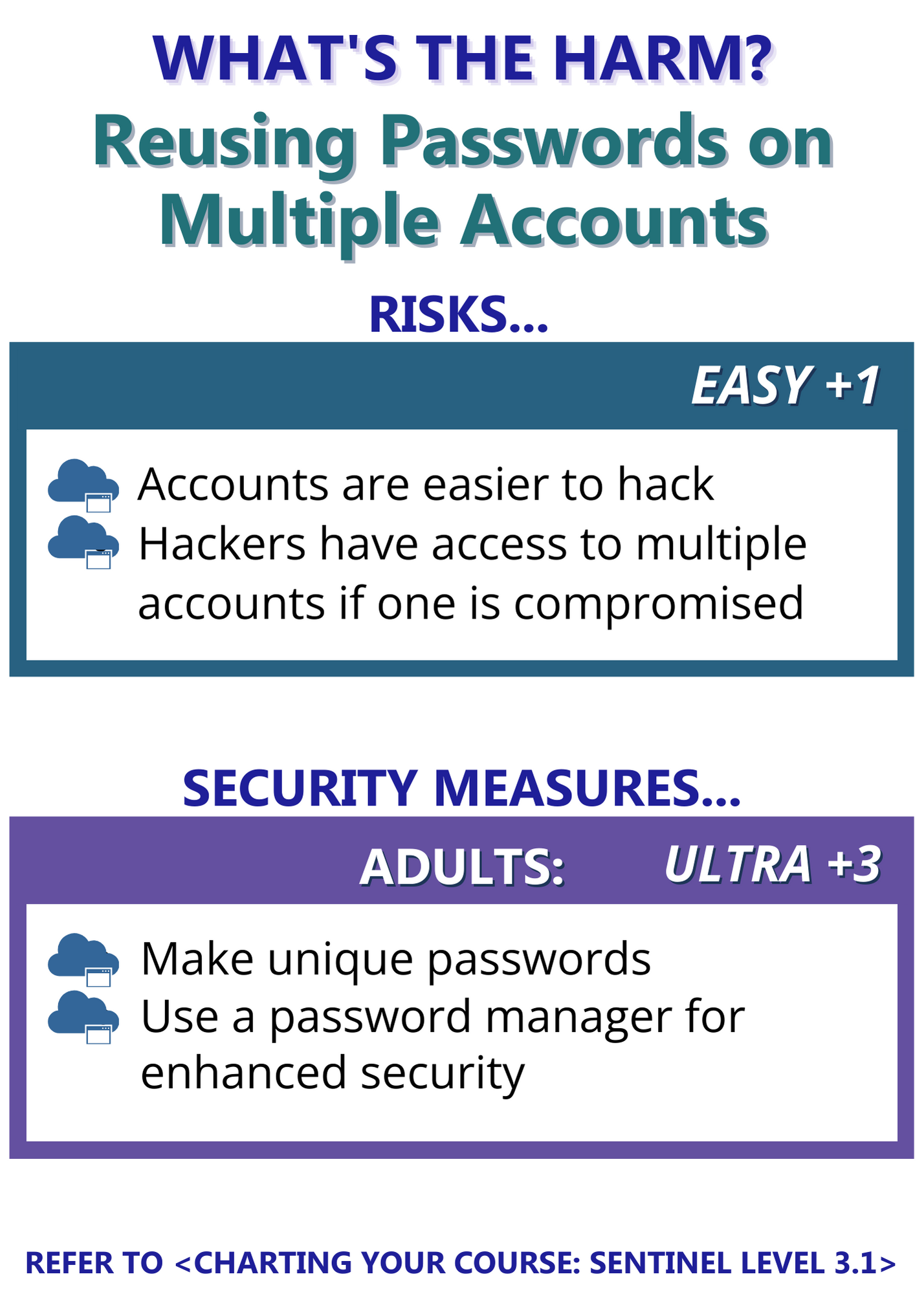
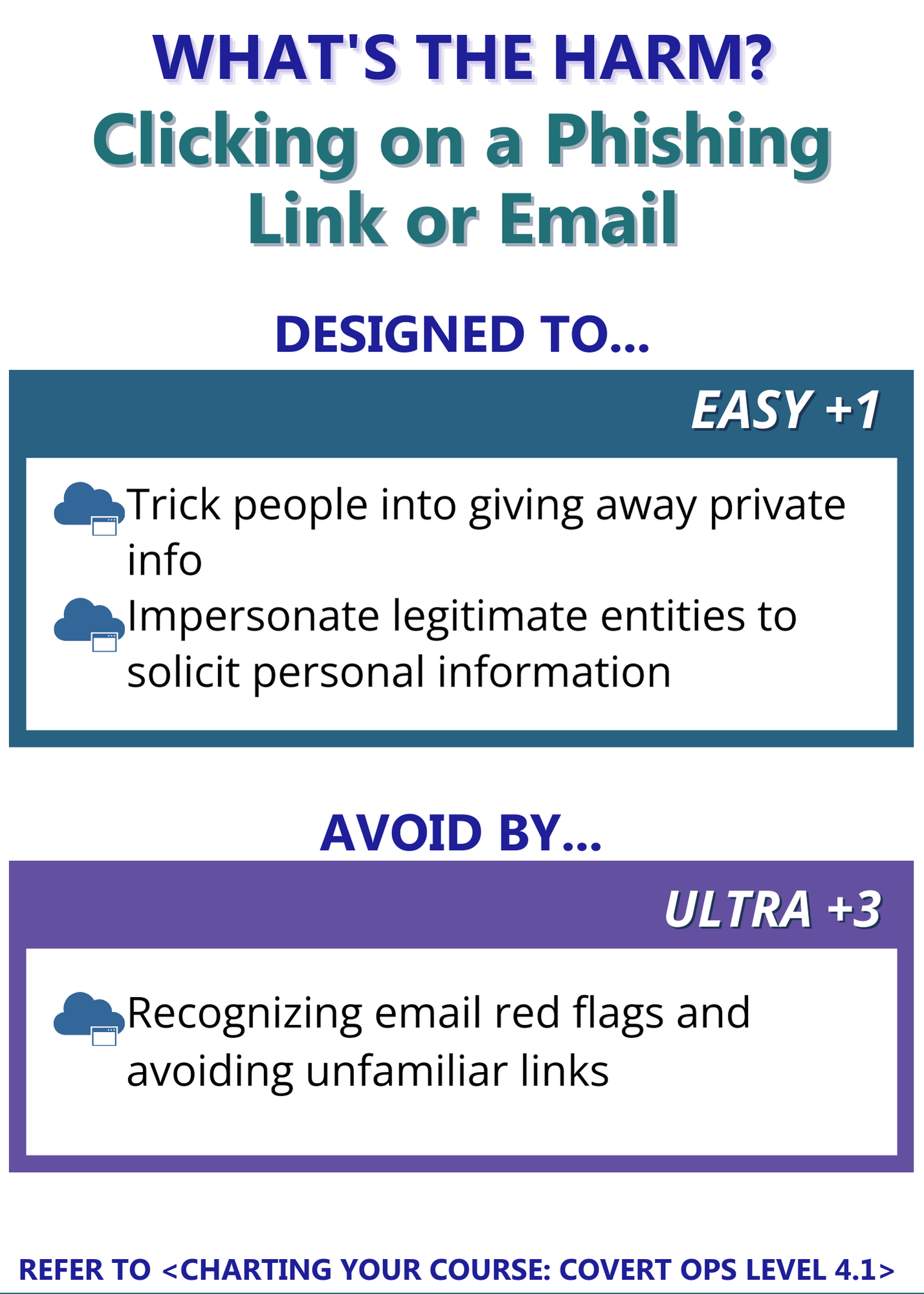
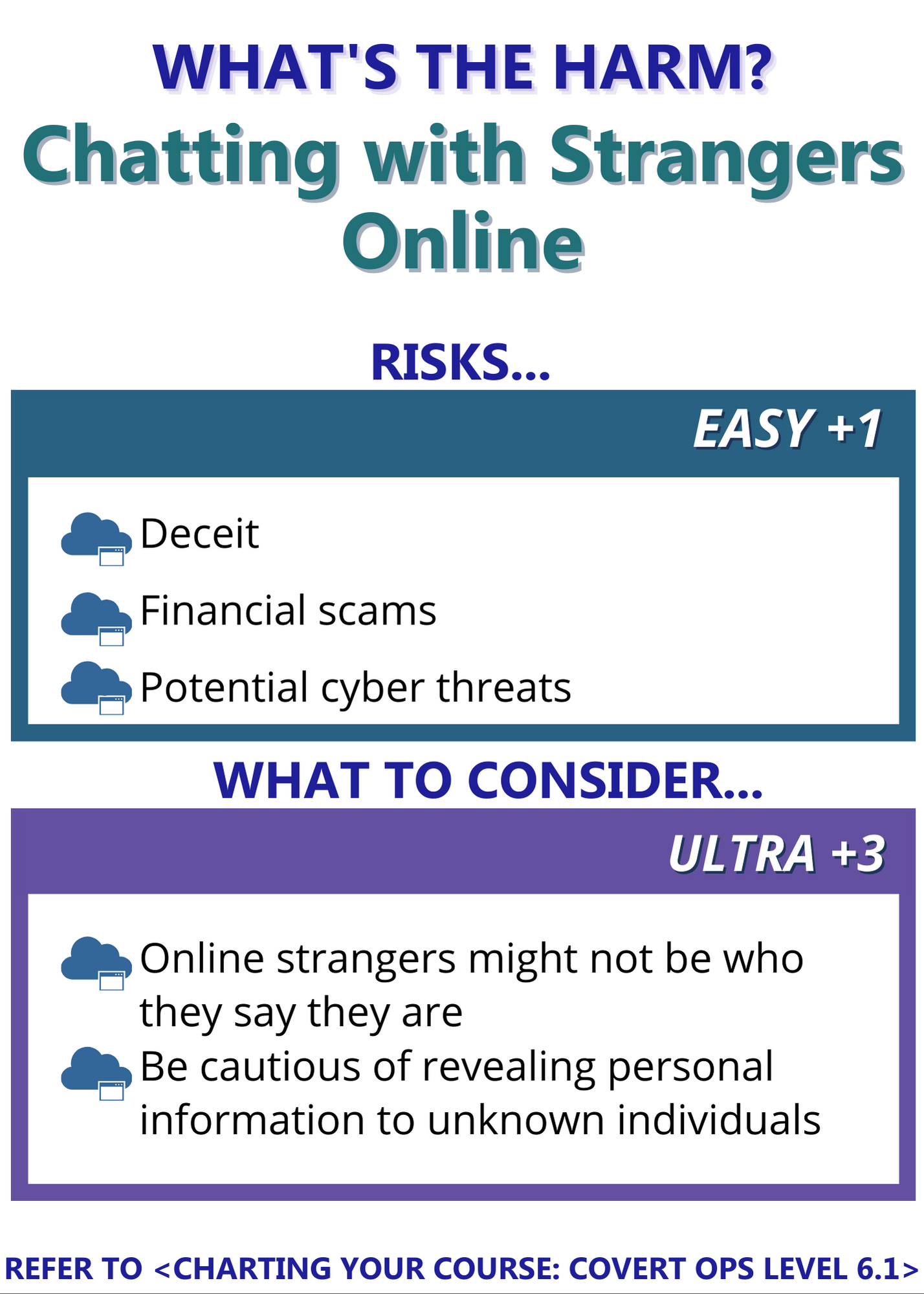
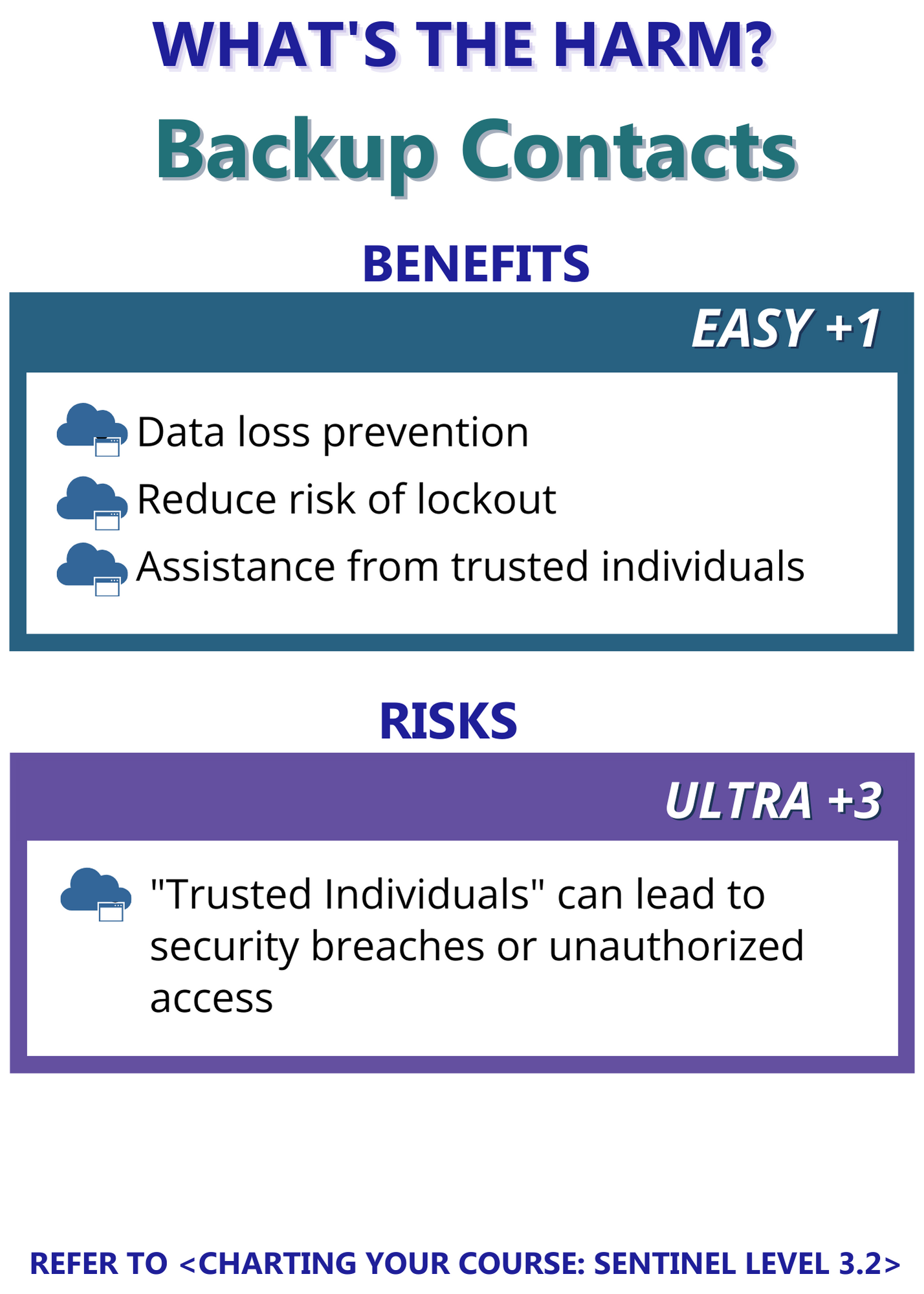
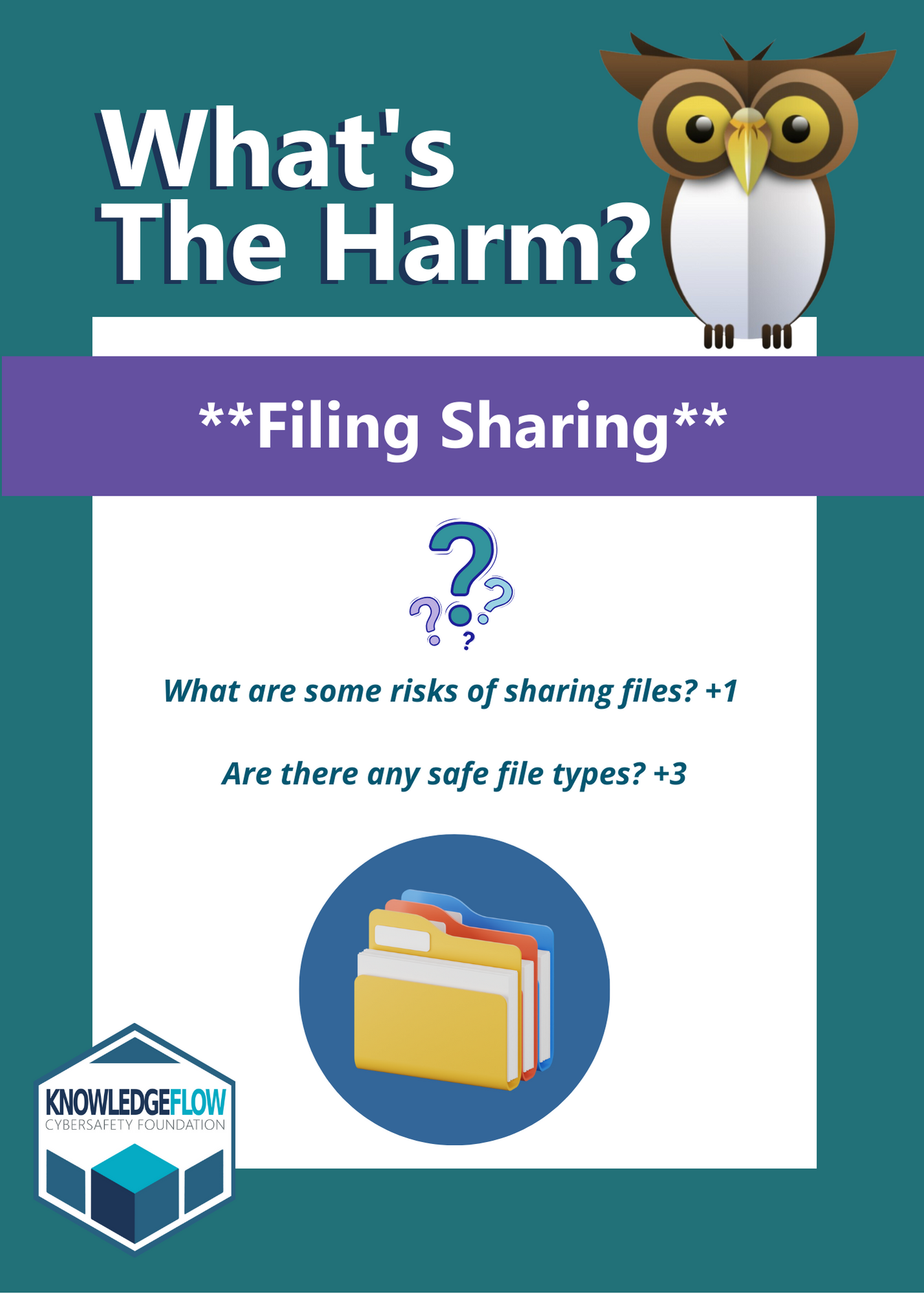
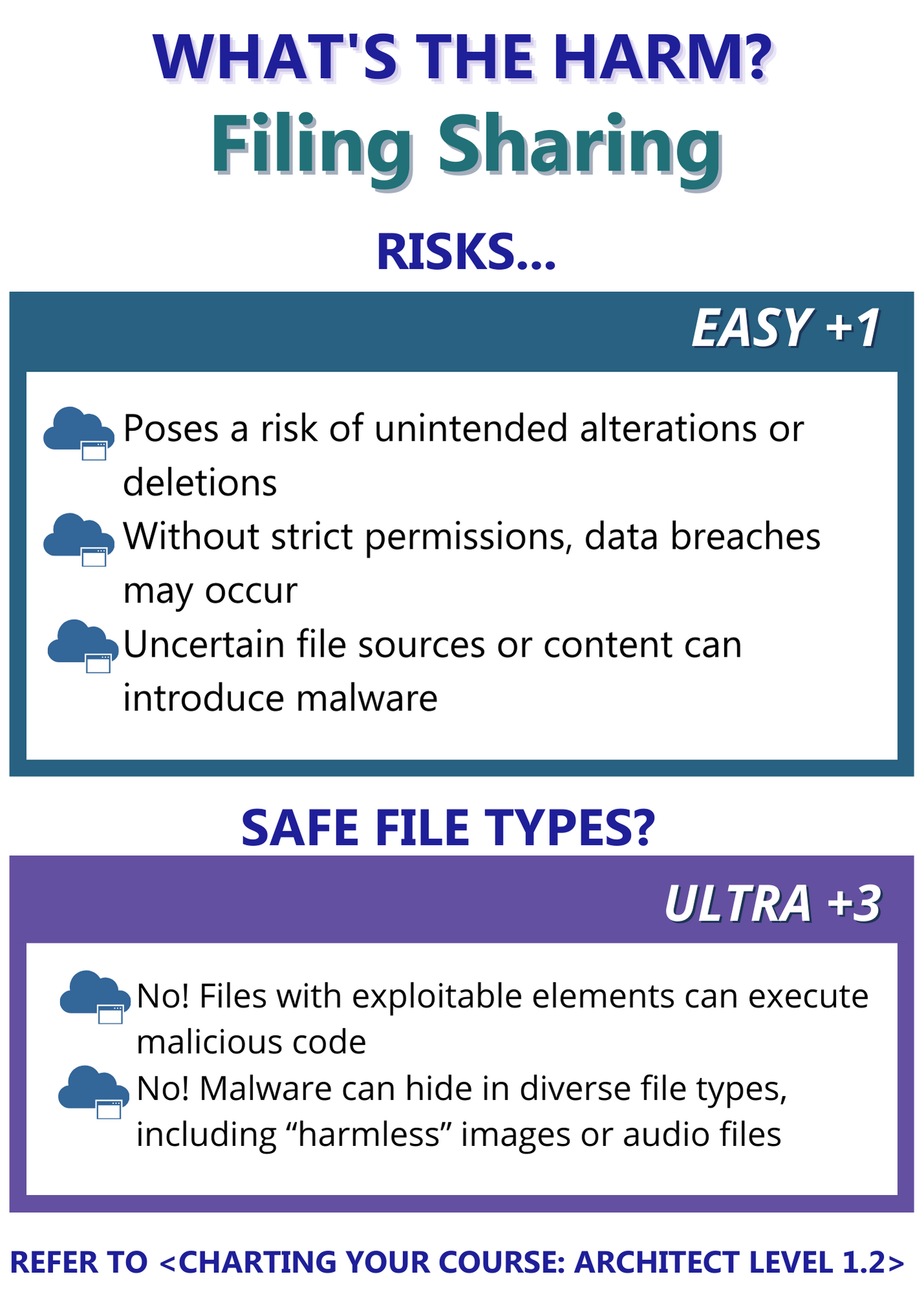
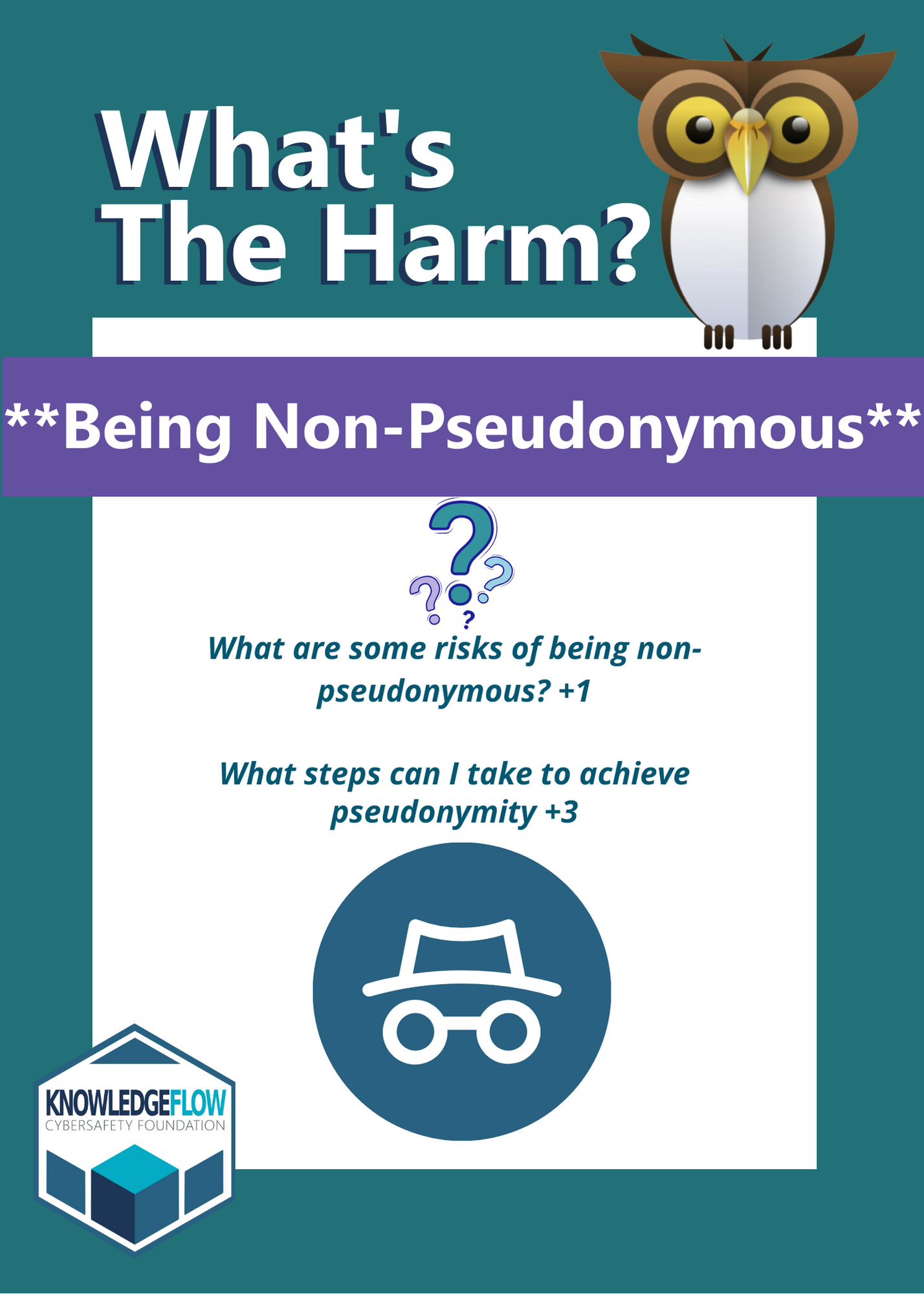
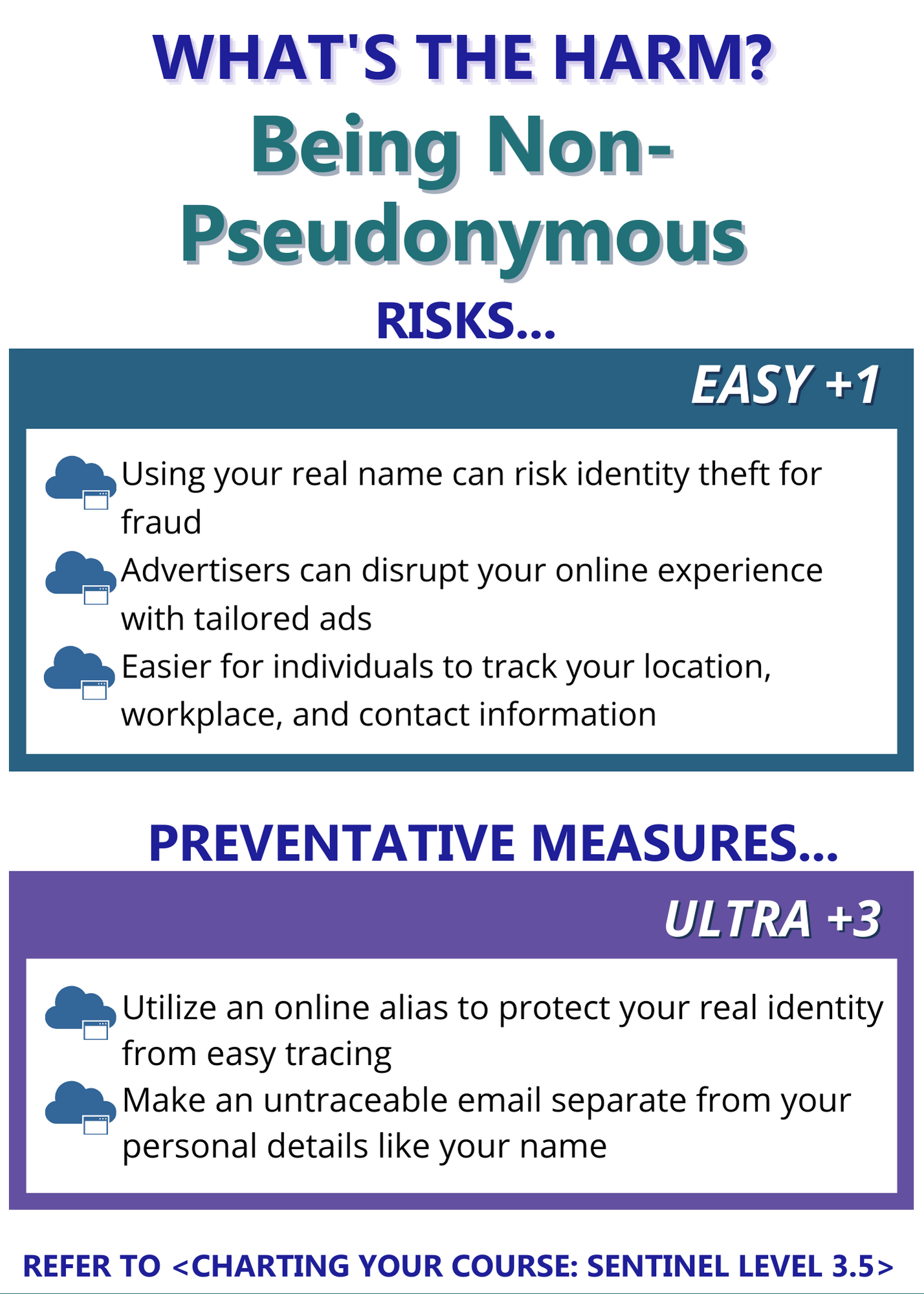
Ready to put your cybersituational awareness skills to the test? Dive into “What’s the Harm: Charting Your Course,” a single and multiplayer flip card game designed to sharpen your knowledge about the risks of online practices. Challenge yourself and others to navigate the digital landscape safely while having fun. Are you up for the challenge? Enhance your cybersecurity skills and play today!
Learn more ways to keep safe online!
Check out our available courses down below.

1. Play Instructions
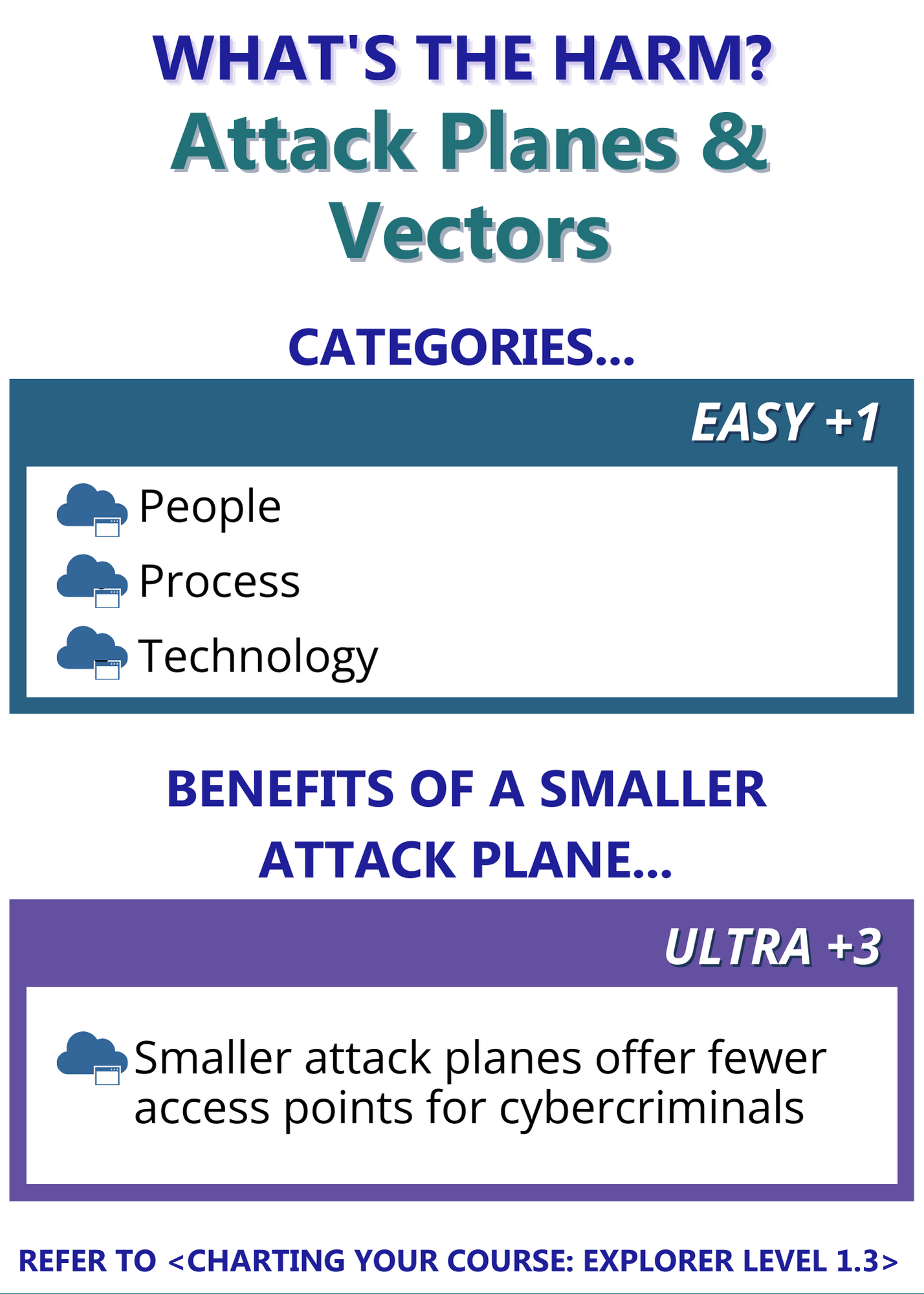
Get ready for a challenge that will sharpen your knowledge about the risks of online practices.

A. Single Player
Here’s the game plan: Start by reading the questions on the front of each card and jotting down your answers. Then, flip the card to see if you hit the bullseye! Don’t forget to keep track of your score for each correct answer on the sleek scorecard provided.
B. Multi Player
Here’s the game plan: Divide your group into teams of 2 or more players. Team A starts by picking a card and reading the question on the front of that card. Team A gives their answer to Team B who flips the card to see the recommended answer and scores Team A’s answer on the scorecard based on how many points the answer included. Then Team B repeats the same steps and Team A scores their answer.
2. The Scorecard
Print as many scorecards are required based on the number of teams/individuals playing.
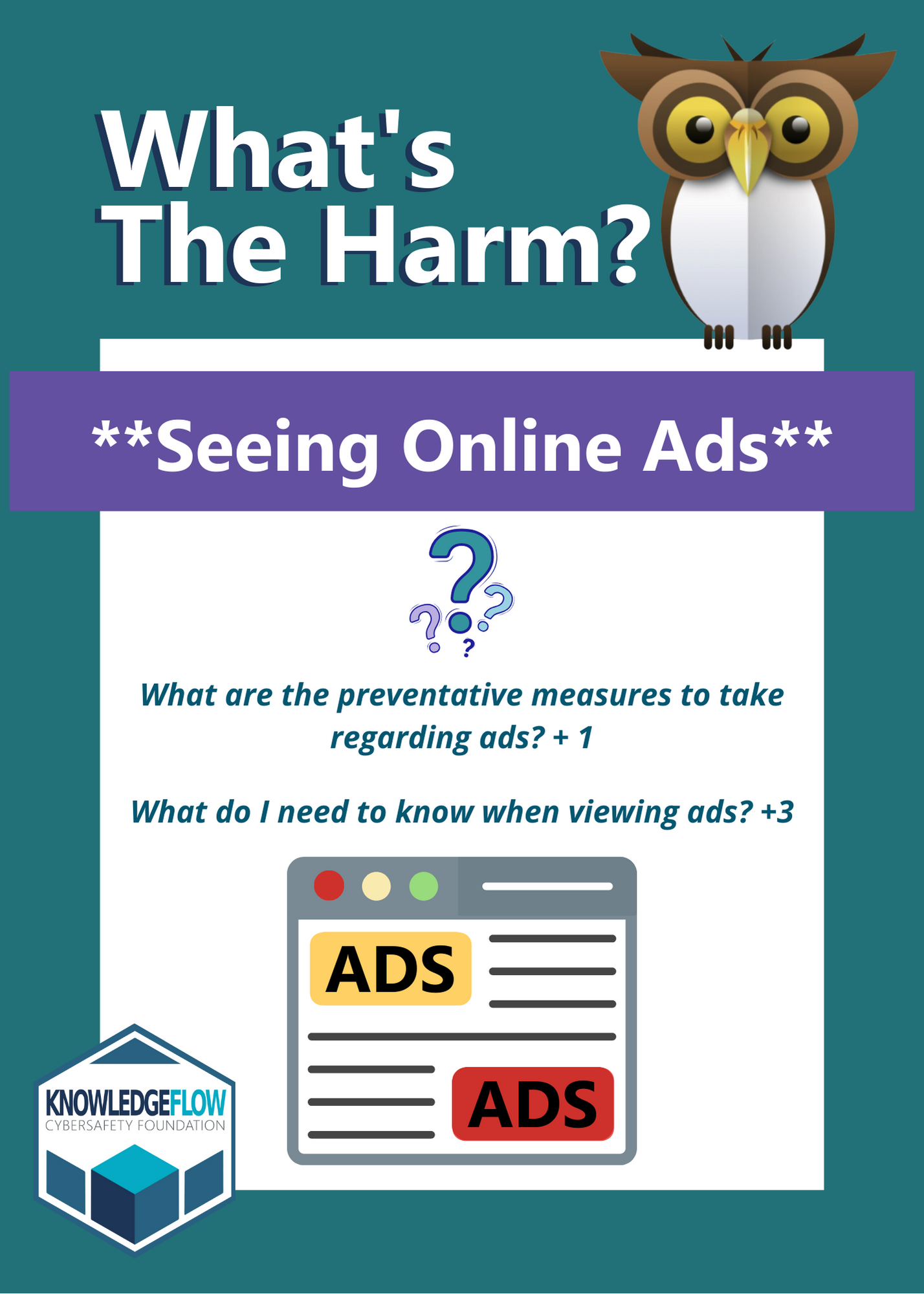
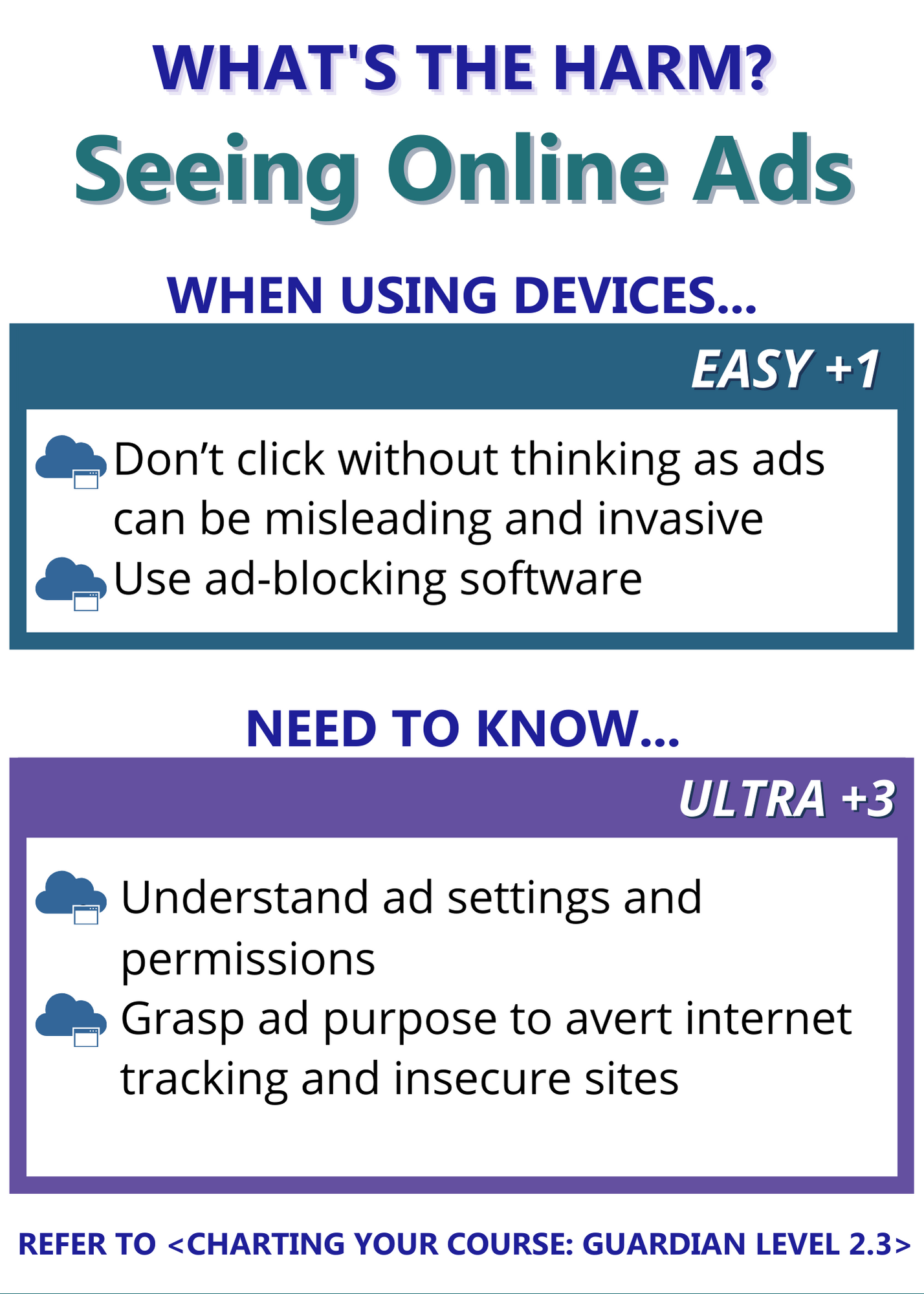
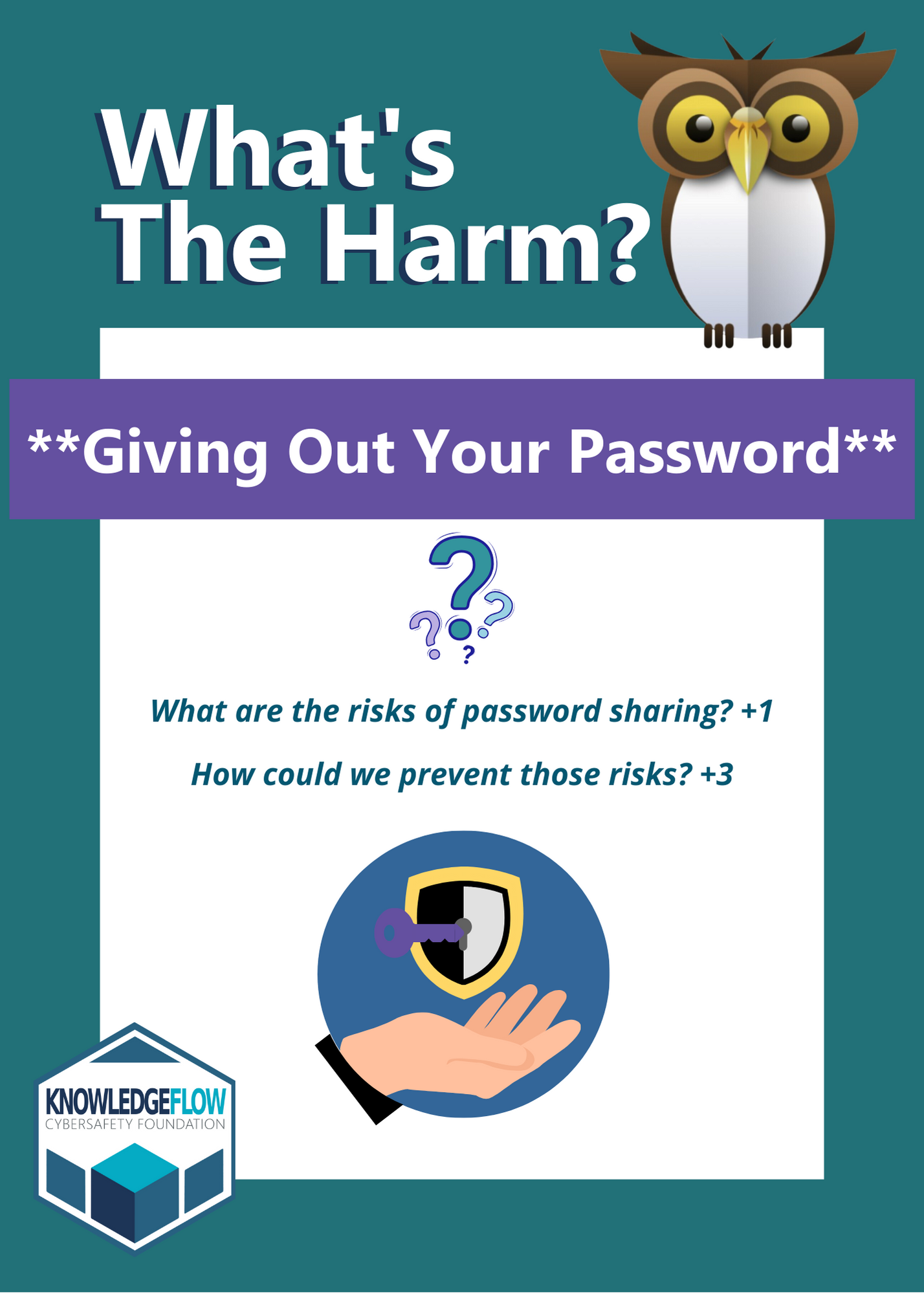
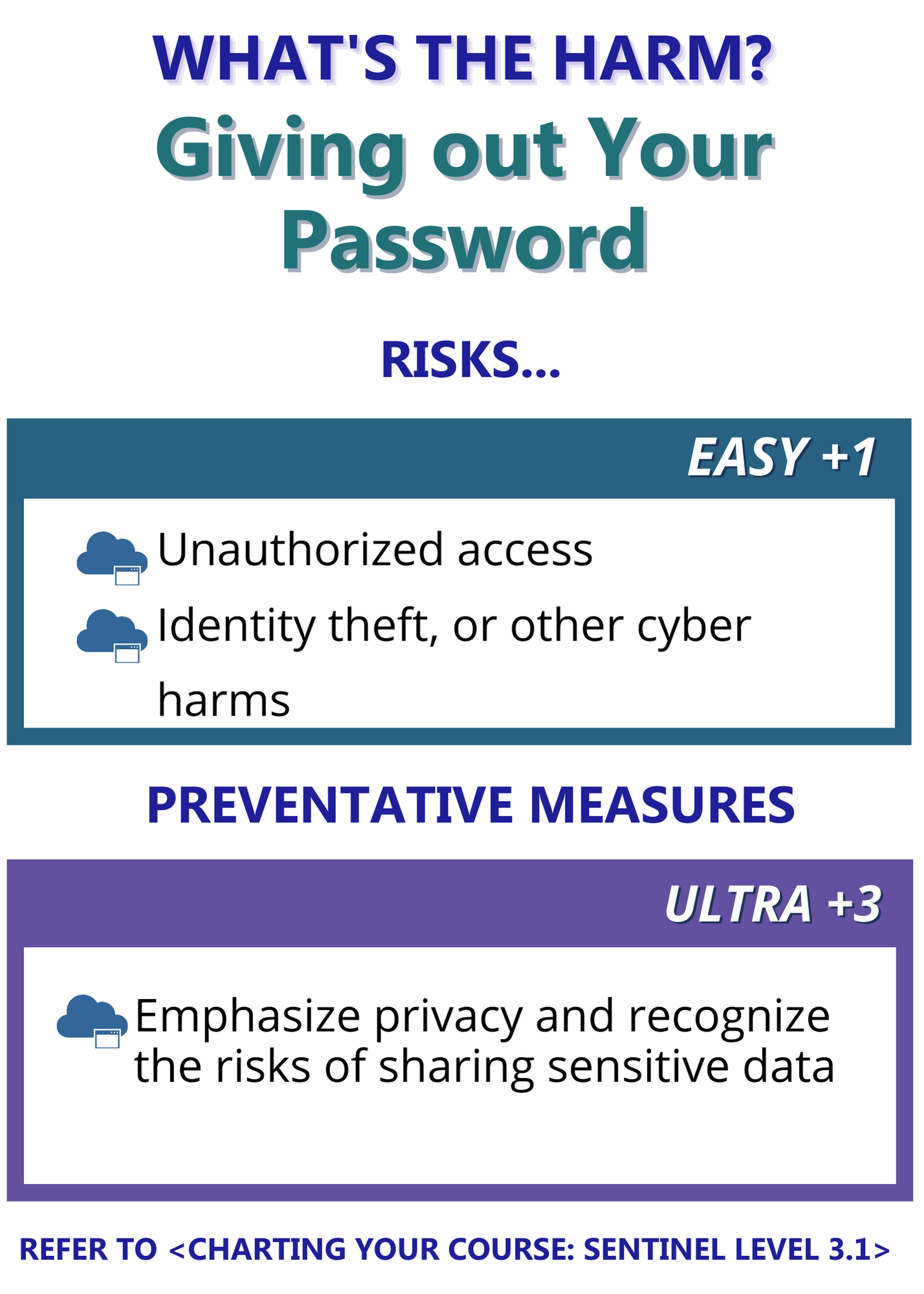
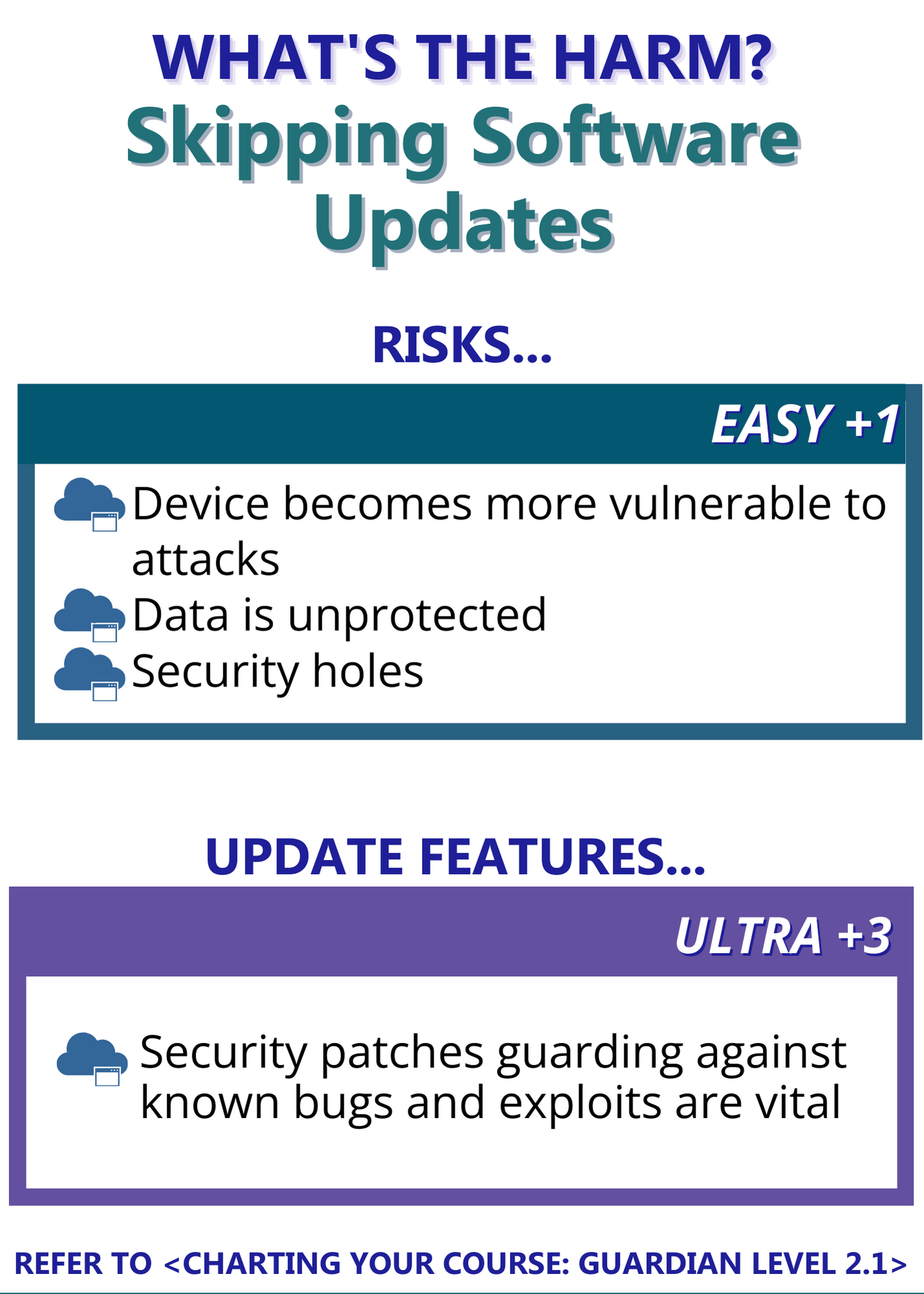
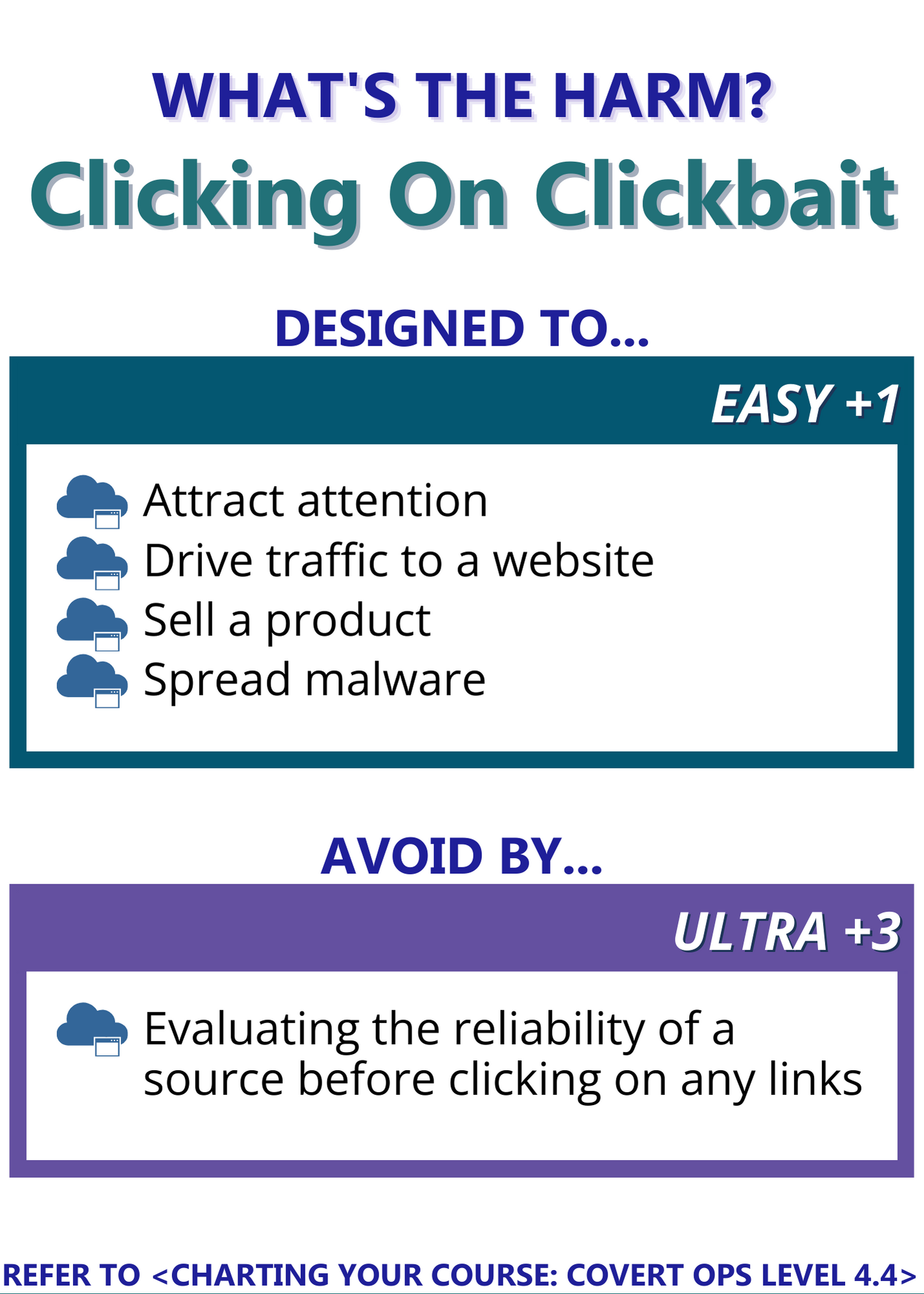
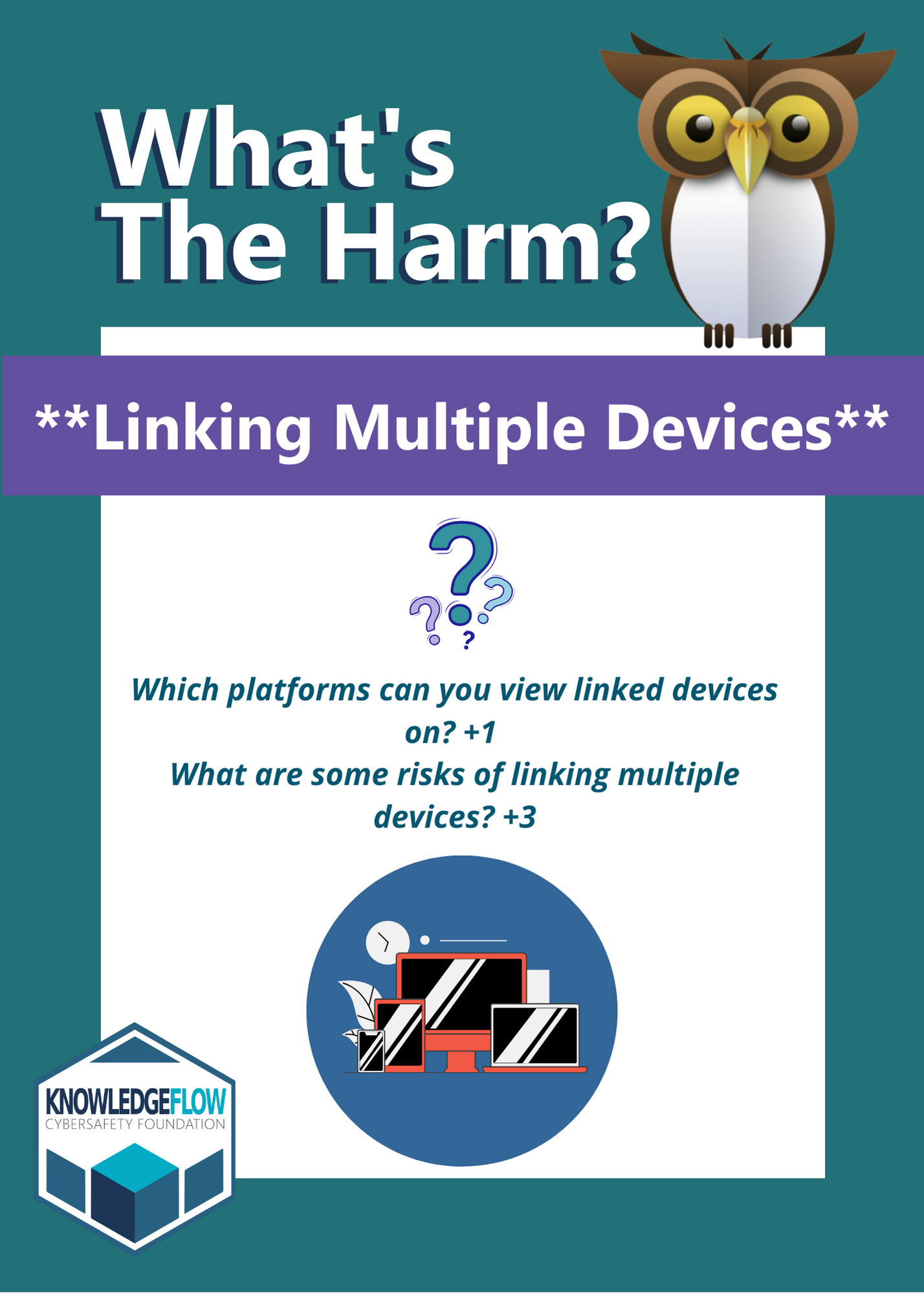
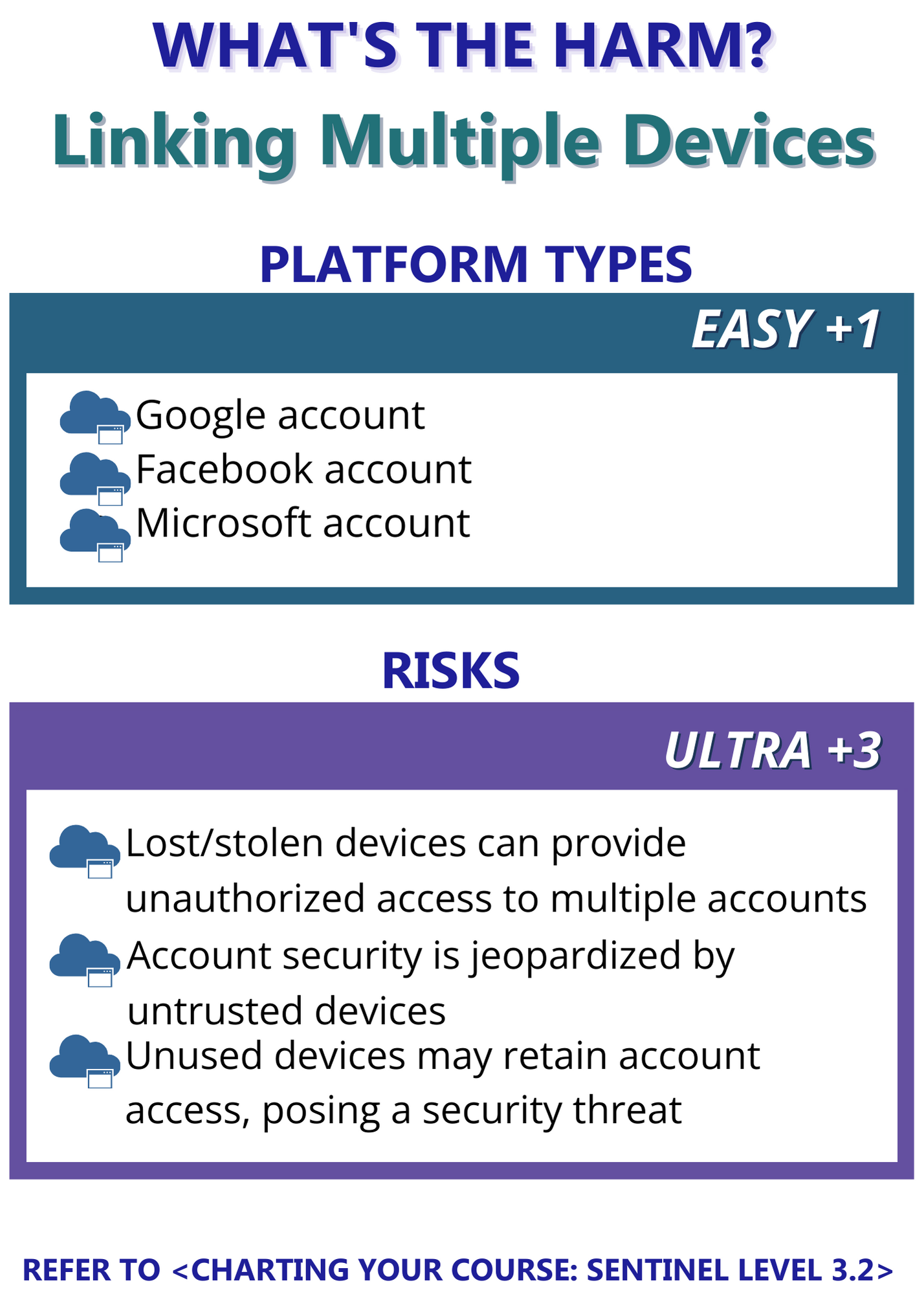
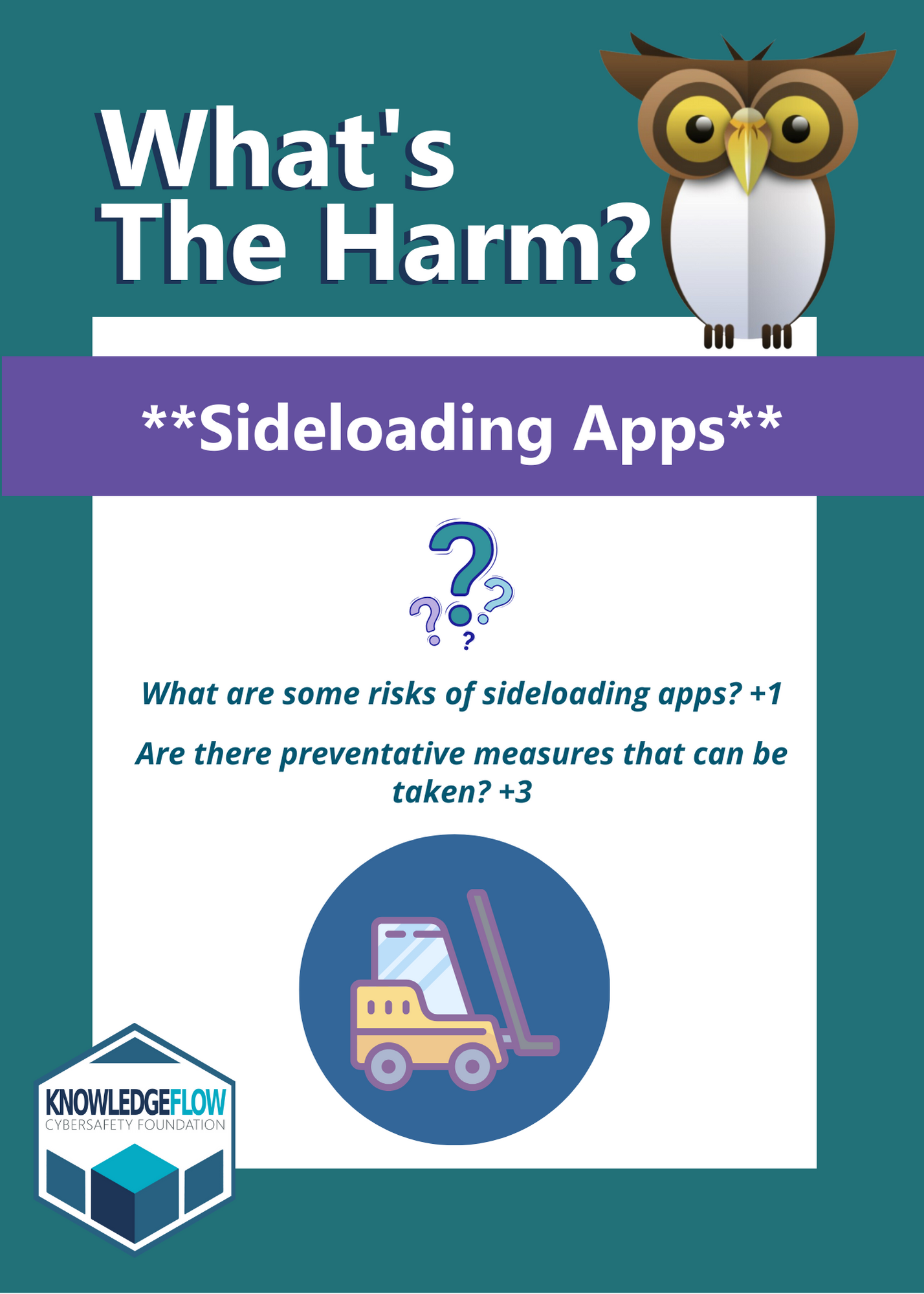
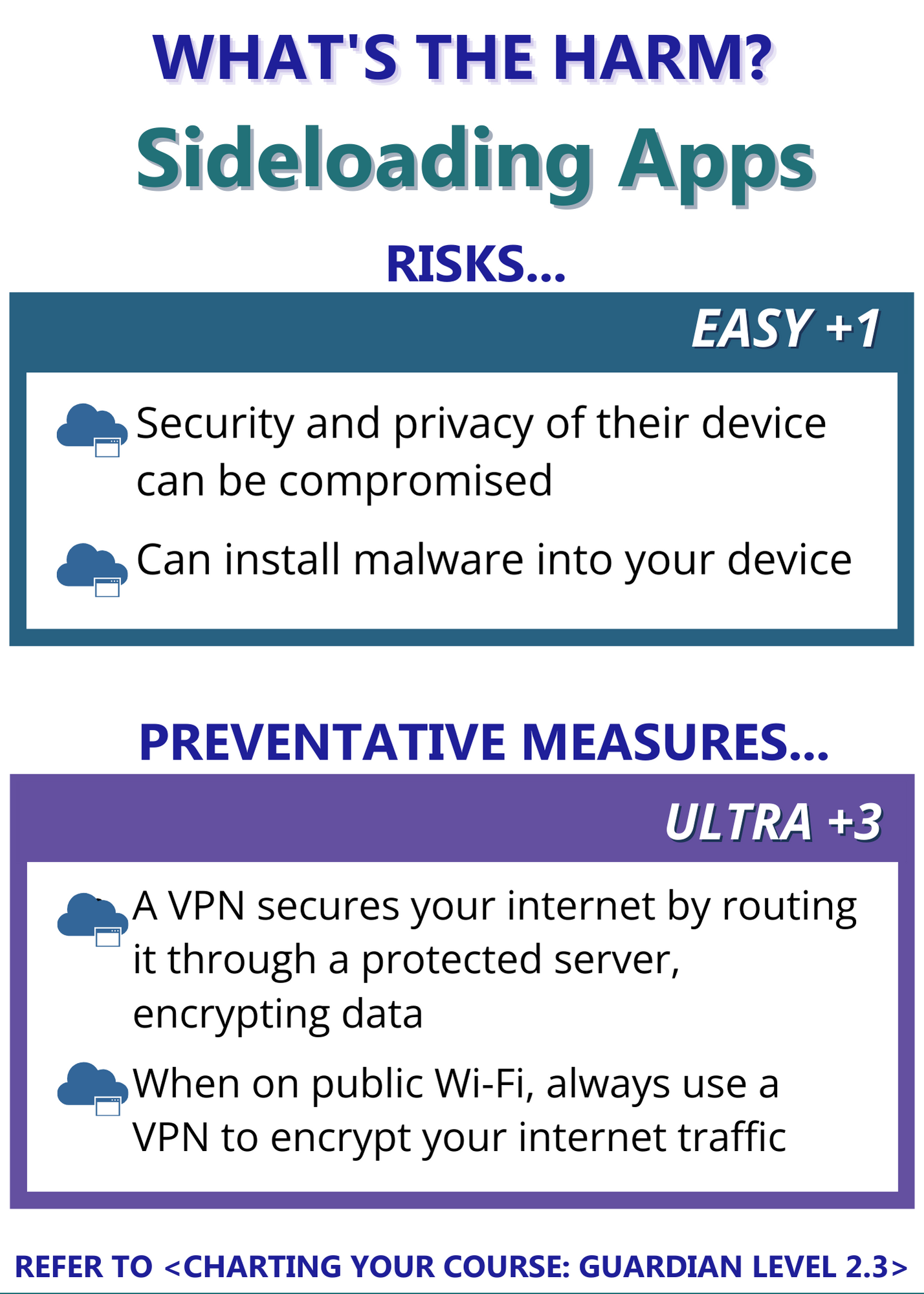
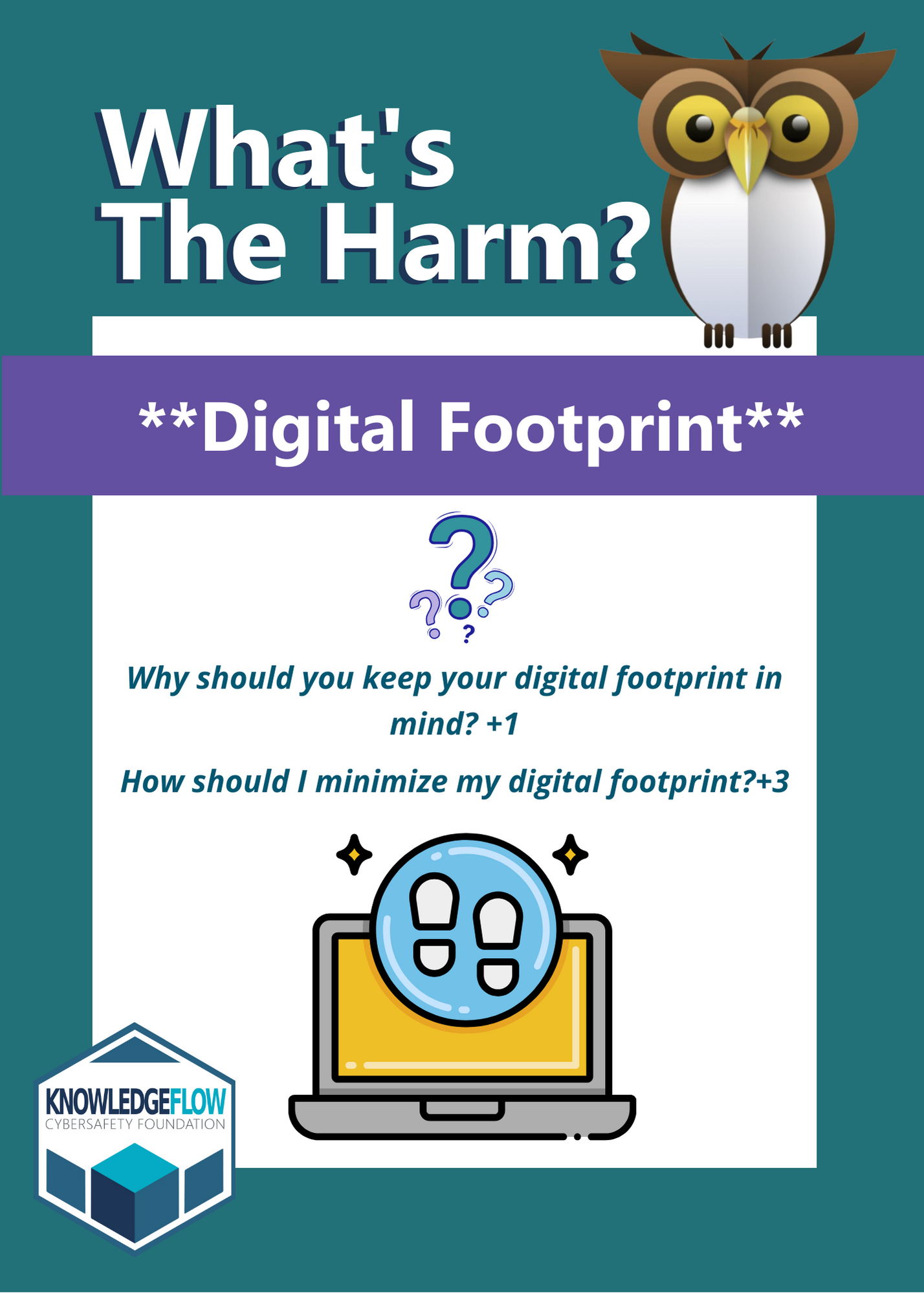
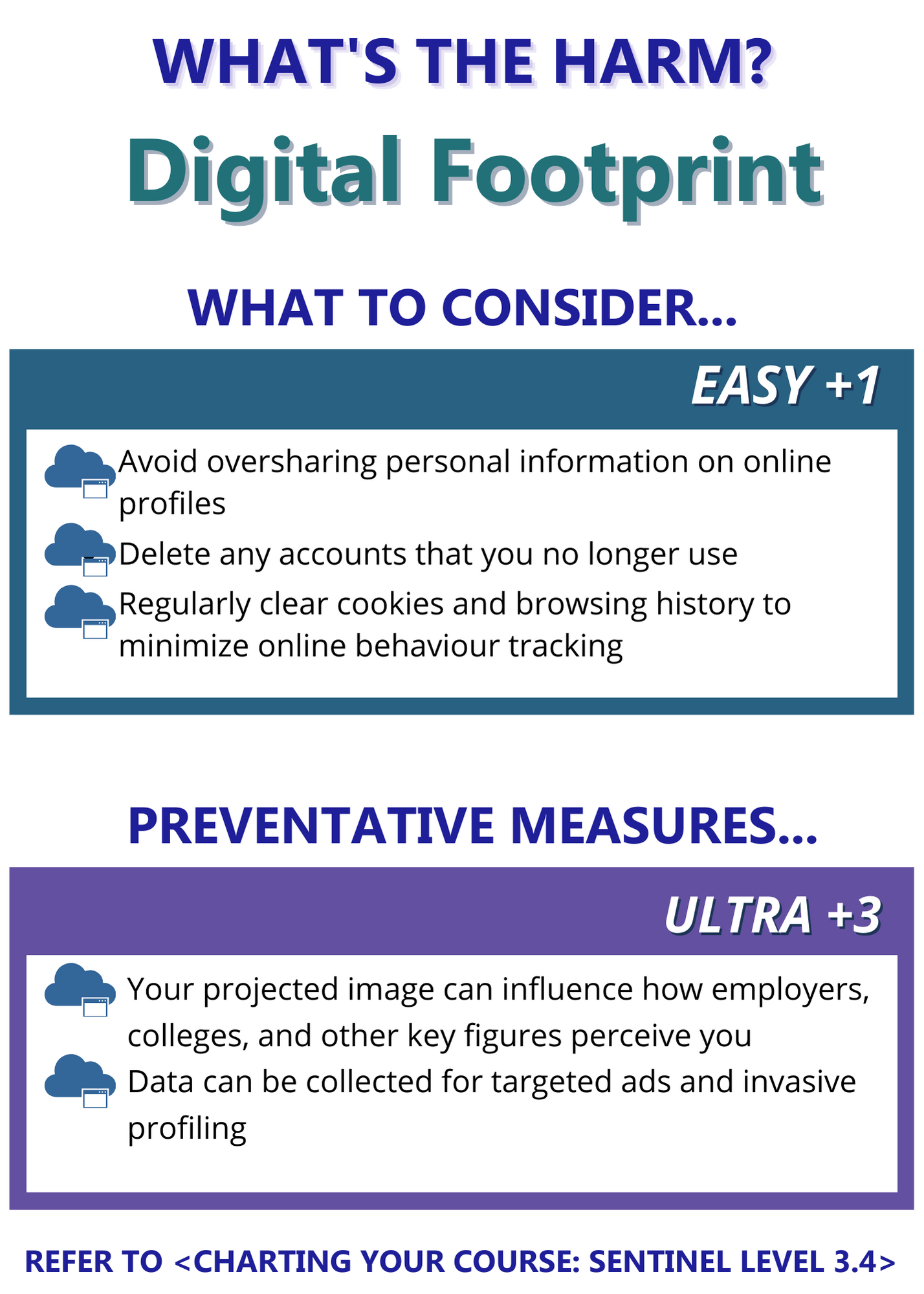
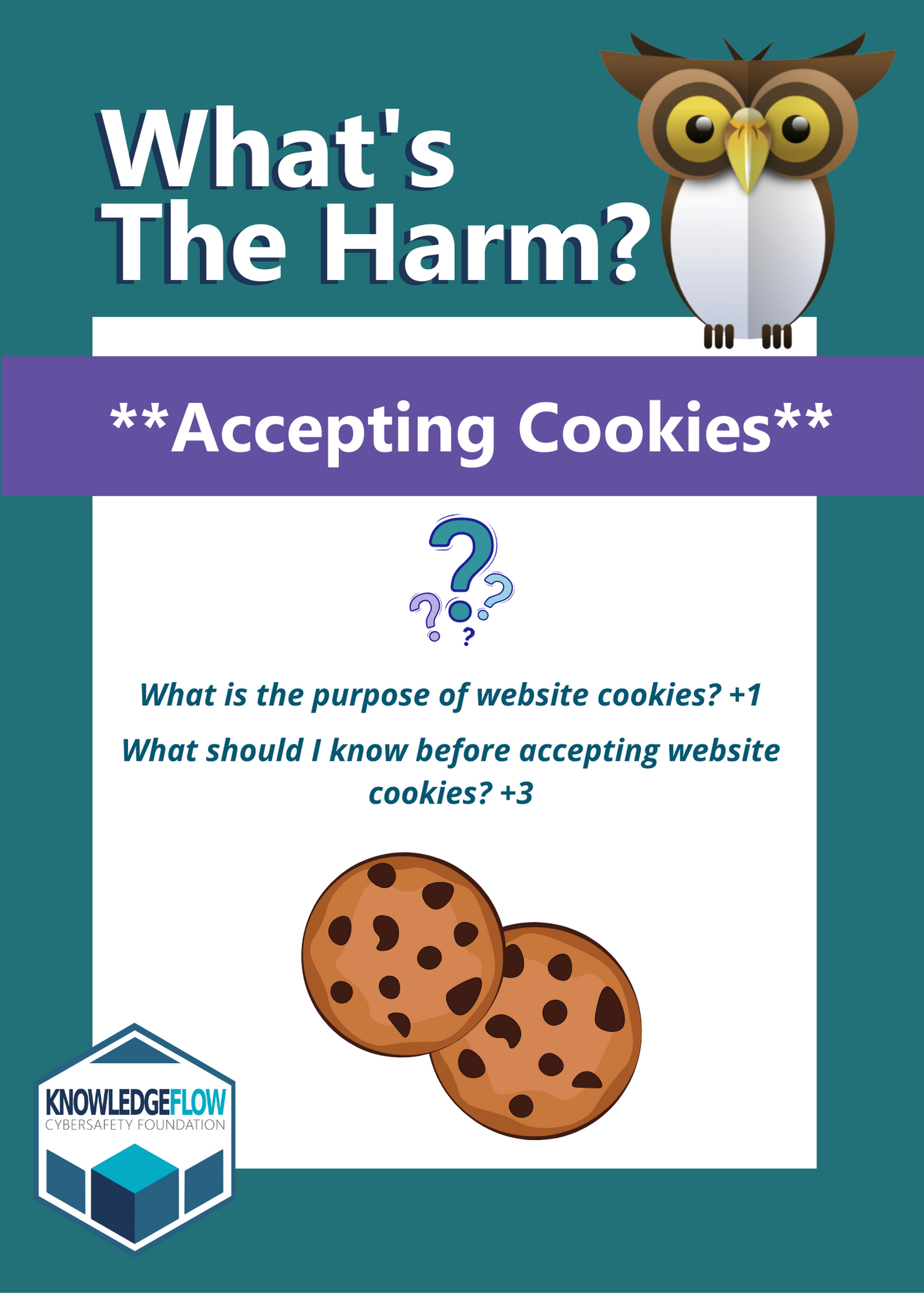
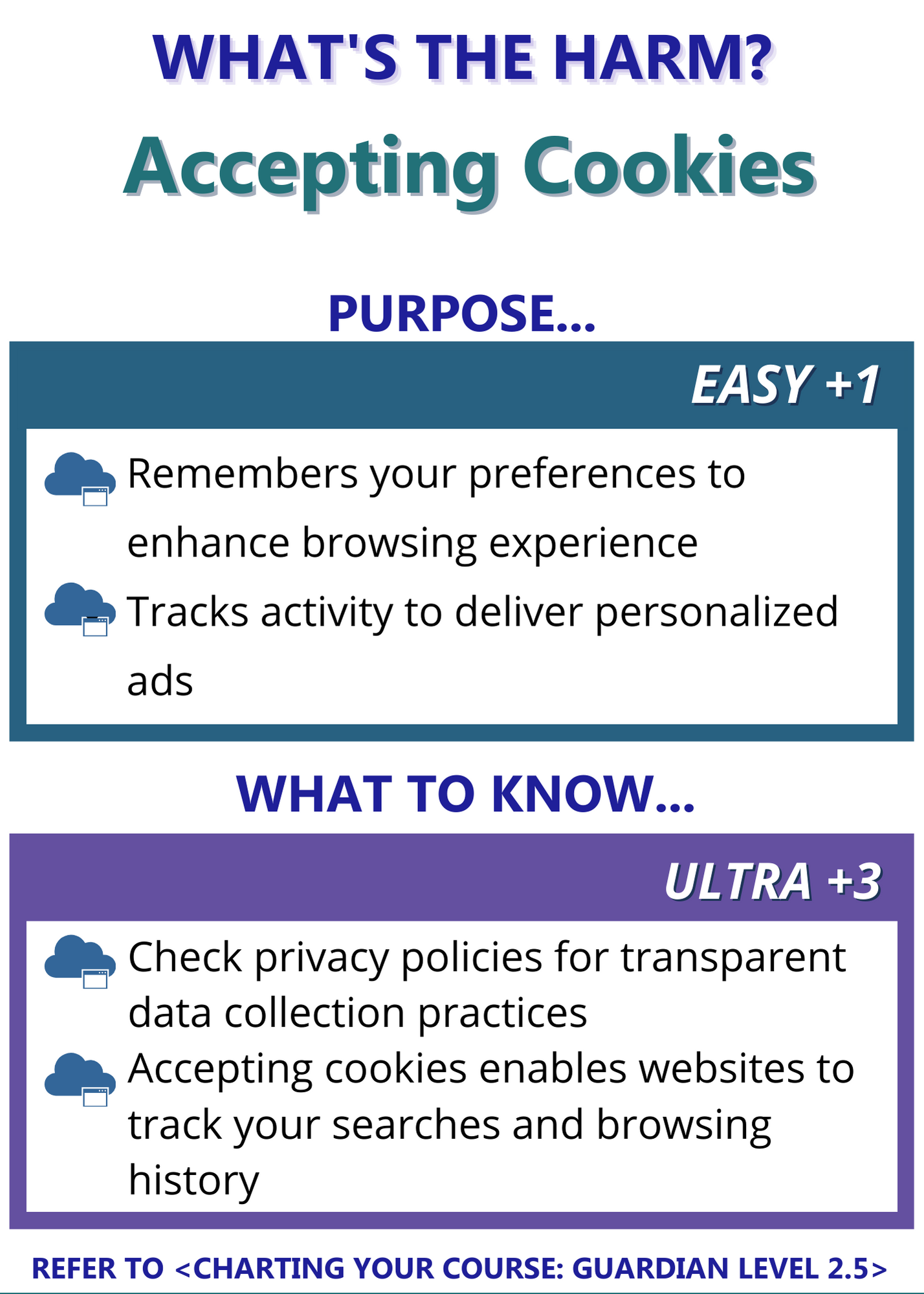
3. The Game: What’s the Harm: Charting Your Course

platform for teachers
Cybersafety for your classroom
At KnowledgeFlow, we emphasize the significance of cybersafety education for both educators and students. Understanding and teaching essential cyber safety practices can protect both teachers and students from online risks. By fostering safe technology use in the classroom, students can learn to navigate the digital world securely. Learn how to create #UnHackable classrooms!